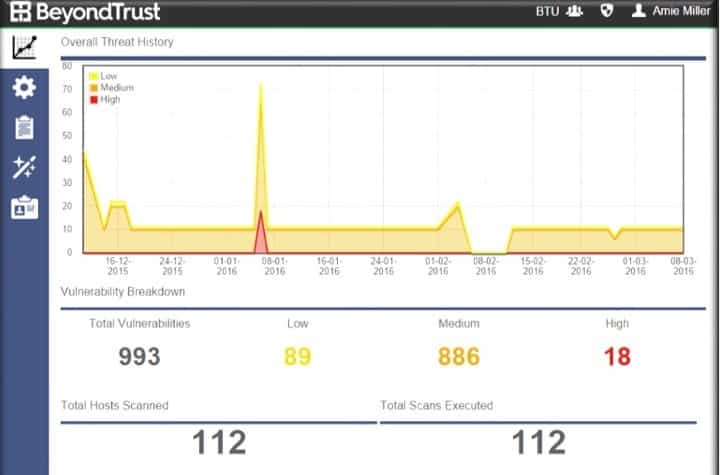
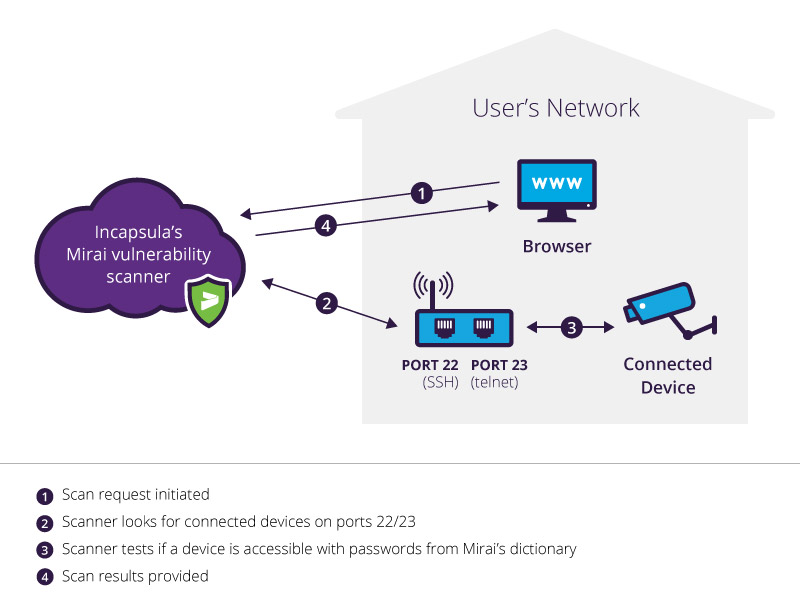
GitHub - billy-osullivan/IOT-Protect-Continous-Vulnerability-Scanner: A continous vulnerability scanner which scanys for Qbot and Mirai vulnerabilites and displays results in a browser
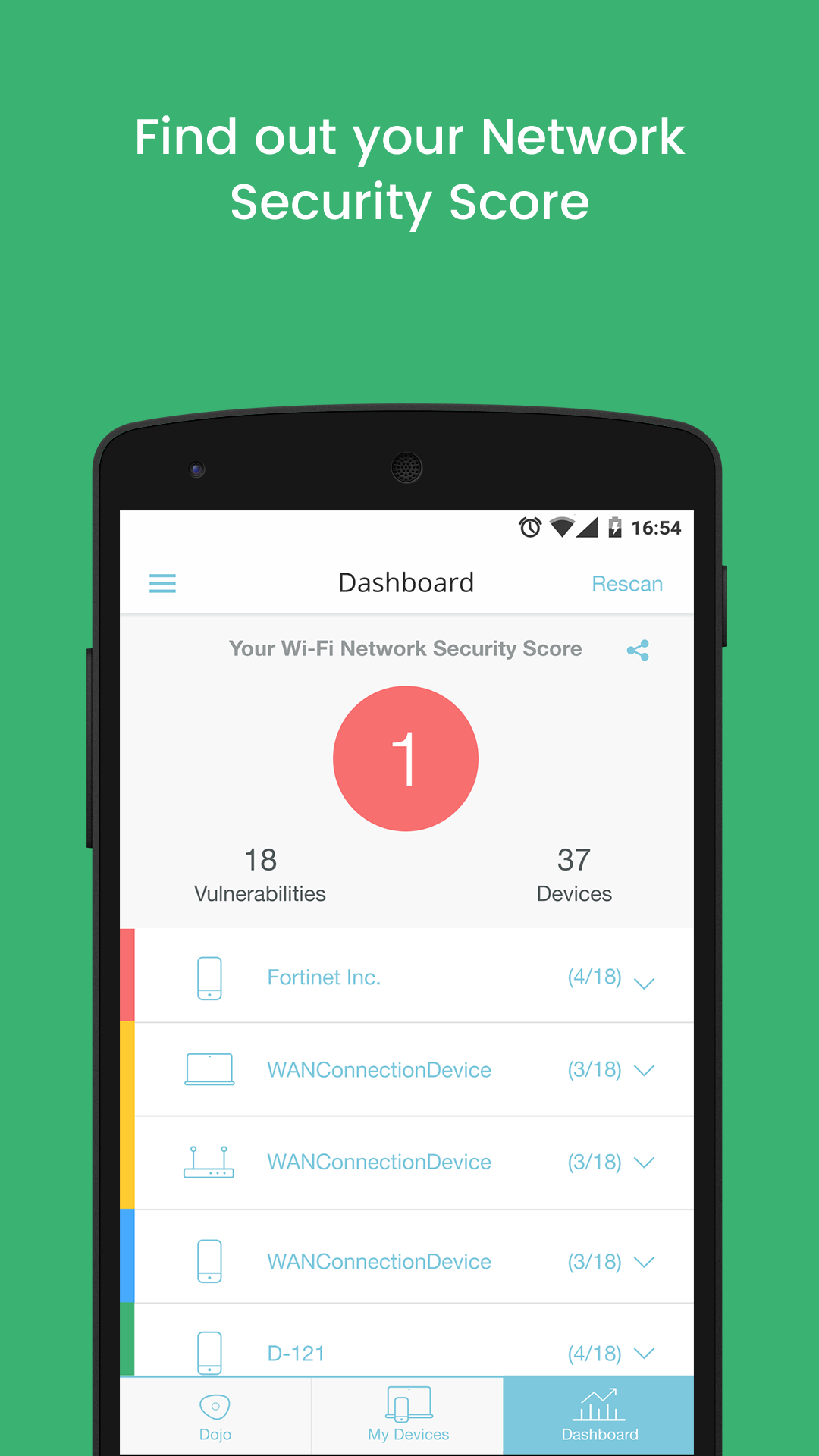
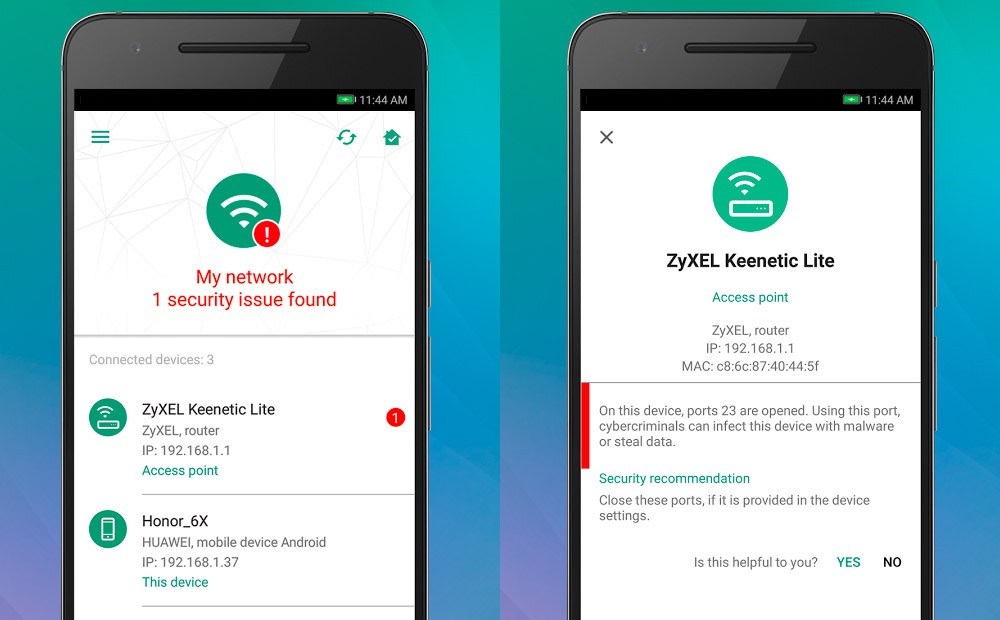
New Dojo Intelligent IoT Vulnerability Scanner App Provides Consumers With Deep Insight Into The Cybersecurity Risks In Their Smart Homes